Knowledge Base
Active Directory (AD)/ LDAP connector on-premise
- Create a cloudplan group on your LDAP / AD server, e.g. “cloudplan” and assign this group to all users who should be able to log in to cloudplan as a user. Please note when creating new users, that the password can not be changed via cloudplan when choosing “User must change password at next logon” under “Password options”. The user must therefore change this password, e.g. via his work computer. Every user to be imported must have an e-mail address.
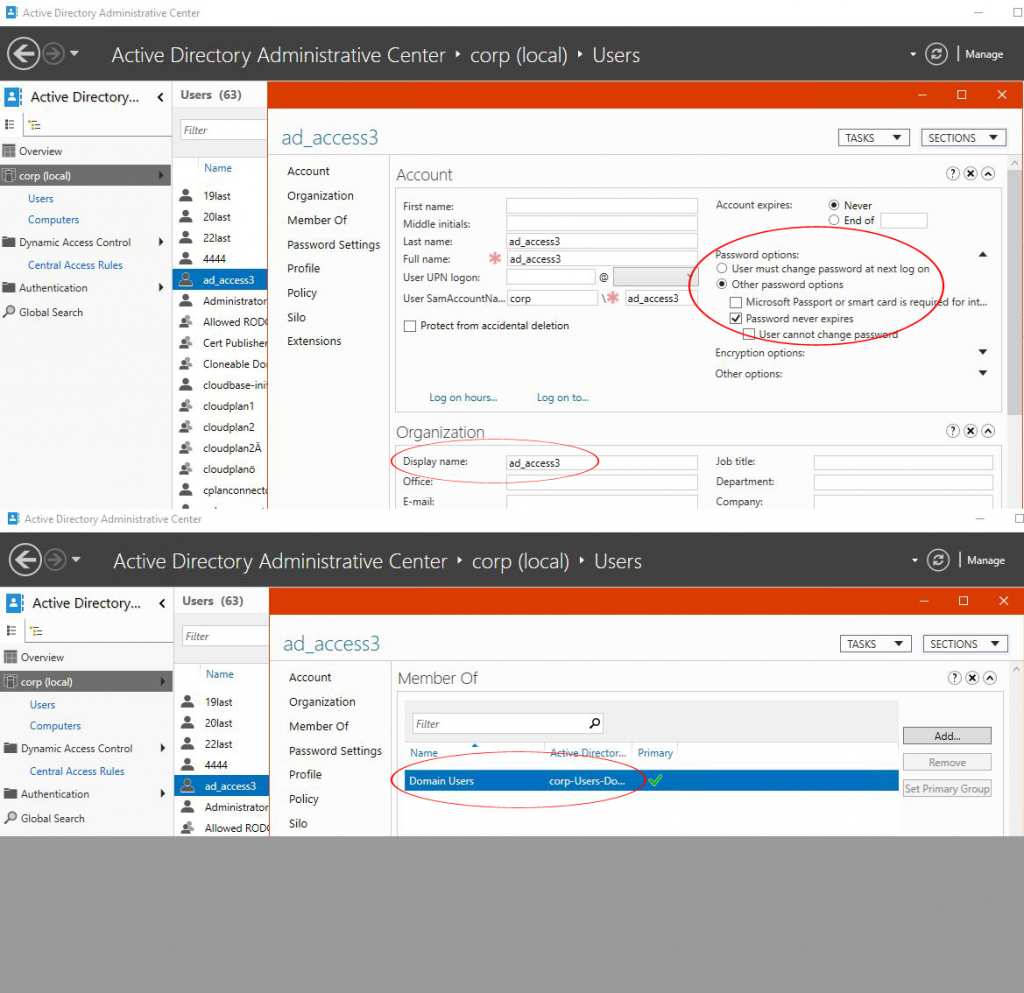
- Please create a user on your LDAP / AD server to read user data. This is used by the cloudplan connector to perform the authentication. The field “Display name” must contain the name of the user (see screenshot). Please change the password settings to “Other password options”, then “Password never expires”. If necessary, you can manually change this password at any. You must then reinitialize it in the cloudplan portal thereafter. You reenter the password with the user name in the portal under “AD / LDAP”. The newly created user must be “member of” “domain user” “primary”, this is also the automatic setting when creating a new user.
- Run a cloudplan enterprise license on a windows machine within the network location of the LDAP/ AD server. It is recommended to operate the connector as a dedicated server in order to prevent impairment of user authentication.
- Under https://portal.cloudplan.net/ldap create a new LDAP connector
- Choose the windows machine with the enterprise license running
- Insert the address of the LDAP server
- Insert the AD/ LDAP username and password that has the appropriate rights to read LDAP users on your server.
- Create a group that is equal to the group assigned to the users in step 1) on your LDAP server
- Run “Sync users” so that the users are made available to the cloudplan system. Or wait until the frequent synchronisation every hour. You will find the next execution time in the portal under the menu “AD / LDAP”.
- Finished! All user requests for the LDAP group members will be directed to your LDAP server for authentication.
- Hint: Users that are created directly within cloudplan will be authenticated only through cloudplan, not via the LDAP server.